The content material of this submit is solely the duty of the creator. AT&T doesn’t undertake or endorse any of the views, positions, or info supplied by the creator on this article.
In our previous blog, we explored the importance of host discovery strategies utilizing Nmap, Netdiscover, and Indignant IP Scanner. Now, let’s dive deeper into the community reconnaissance and focus particularly on the highly effective options supplied by Nmap.
Famend for its versatility and sturdy characteristic set, Nmap allows analysts to probe networked methods, map community topology, determine open ports, detect companies, and even decide working system particulars. Its command-line interface, coupled with a myriad of choices and scripting capabilities, makes it an indispensable asset for safety professionals, community directors, and moral hackers alike.
I’ve used a digital surroundings created primarily for demonstration functions to see these scanning strategies in motion, Goal machine for this demonstration is metasploitable2 (192.168.25.130), Attacker Machine is Kali Linux (192.168.25.128). We have already got seen find out how to uncover hosts in a networked surroundings in our earlier weblog. Moreover, you possibly can discuss with nmap.org for higher understanding of those strategies.
Let’s check out totally different strategies nmap affords:
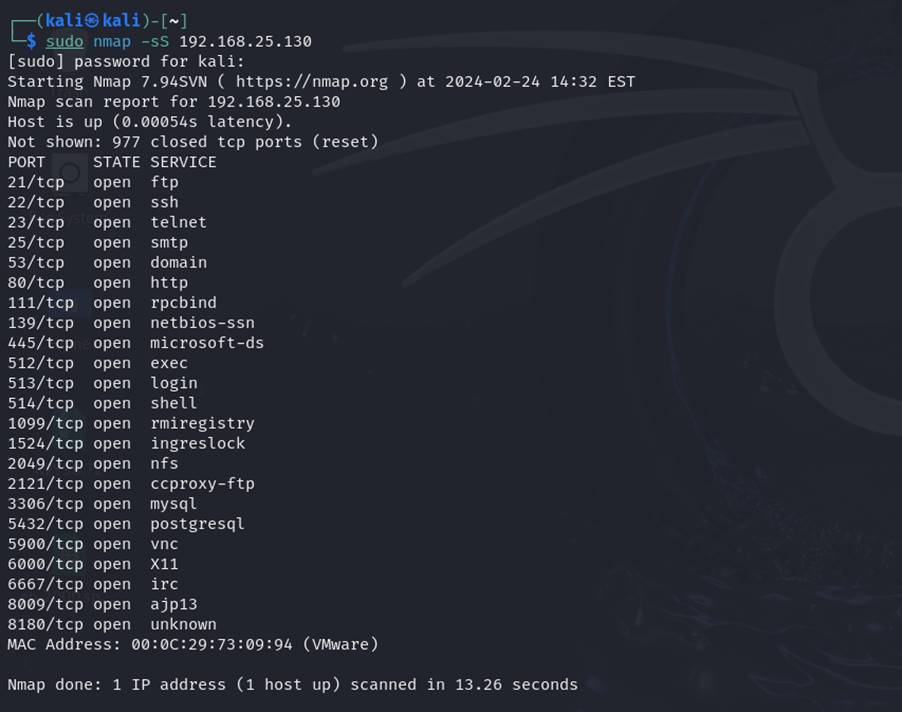
1. TCP SYN scan (-sS):
The TCP SYN scan, also called a half-open scan, sends SYN packets to focus on hosts and analyzes responses to find out if the host is alive. This method is stealthy and environment friendly, because it doesn’t full the TCP handshake, thereby minimizing detection by intrusion detection methods (IDS).
Syntax: sudo nmap -sS target_ip
![TCP SYN scan]()
2. UDP scan (-sU):
The UDP scan sends UDP packets to focus on hosts and analyzes responses to determine open UDP ports. This method is especially helpful for locating companies that won’t reply to TCP probes.
Syntax: sudo nmap -sU target_ip
3. Complete scan (-sC):
The great scan choice, denoted by -sC, allows customers to launch a battery of default scripts towards goal hosts. These scripts embody a variety of functionalities, together with service discovery, model detection, vulnerability evaluation, and extra.
Syntax: nmap -sC target_ip
![co0mprehensive scan]()
Customers can try to examine the output with aggressive scan and different scanning strategies
Aggressive scan (-A):
The aggressive scan choice, denoted by -A, combines numerous scanning strategies corresponding to TCP SYN scanning, model detection, OS detection, and script scanning right into a single command. This scan offers complete insights into goal hosts however could enhance the chance of detection.
![aggressive scan]()
Syntax: nmap -A target_ip
![aggressive scan 2]()
Above photos are partial snapshots of aggressive scan.
Finest practices:
Whereas Nmap affords unparalleled capabilities for community reconnaissance and safety auditing, it’s important to stick to finest practices and moral tips:
Permission and authorization: At all times guarantee that you’ve got express permission to conduct scans on course networks and methods. Unauthorized scanning can result in authorized repercussions and harm relationships with community homeowners.
Scan timing and stealth: Modify scan timing and strategies to attenuate disruption and keep away from detection by intrusion detection methods (IDS) and firewalls. Use stealthy scanning choices, corresponding to TCP SYN scans, to keep up a low profile.
Information interpretation: Analyze scan outcomes meticulously to determine potential safety dangers, prioritize remediation efforts, and validate safety configurations. Train warning whereas decoding findings and keep away from making assumptions primarily based solely on scan outcomes.
Steady studying and collaboration: Community reconnaissance and safety auditing are dynamic fields. Keep up to date with the most recent developments, collaborate with friends, and interact in knowledge-sharing actions to boost your experience and adapt to evolving threats.
Nmap’s wealthy characteristic set, scanning strategies, and scripting capabilities empower analysts to navigate advanced networks, determine potential vulnerabilities, and fortify defenses towards rising threats.