James Rodriguez – Senior Specialist, Cybersecurity
Govt abstract
Over the previous a number of months, AT&T Managed Detection and Response (MTDR) safety operations heart (SOC) analysts have seen a rise within the utilization of phishing emails containing malicious QR codes. In a latest instance, a buyer that was victimized by a phishing try offered the AT&T analysts with an e mail that was circulated to a number of of its inner customers. The analysts reviewed the e-mail and its included attachment, a PDF containing a QR code and an pressing message claiming to be from Microsoft.
When the focused person scanned the QR code, they have been directed to a counterfeit Microsoft login web page designed to reap usernames and passwords. This sort of assault is known as “quishing.”
Sadly, a number of customers fell sufferer to the assault, and their credentials have been compromised. Nevertheless, our analysts have been capable of have interaction with the shopper and information them by means of the right remediation steps.
Encouraging focused customers to behave shortly and scan the code utilizing their cellphone (which regularly shouldn’t be as safe as the remainder of an organization’s community) is a typical tactic employed by menace actors. By doing this, they hope to persuade the person to behave with out considering and forgo correct safety practices permitting the menace actor to bypass conventional safety measures in place on an organization community.
Risk actor techniques
The menace actor used a Home windows authentication setup for multi-factor authentication (MFA) to provoke the assault. The focused customers acquired a phishing e mail indicating MFA wanted to be arrange on their account. The e-mail included a PDF attachment with directions directing them to scan the included QR code, which was malicious.
As soon as the customers scanned the QR code, they have been redirected to a pretend Microsoft sign-in web page on their cellphone. Right here, they entered their reputable login credentials,which have been then saved and made accessible to the menace actor.
Investigation
As soon as the shopper suspected the e-mail was malicious, they contacted the AT&T staff and offered a replica of the PDF file with the included QR code. The staff analyzed the file and the QR code (see Picture 1) and recognized the related vacation spot as “srvc1[.]data/mcrsft2fasetup/index.html.”
Picture 1: PDF file from buyer containing malicious QR code
![PDF with a malicious QR code in it]()
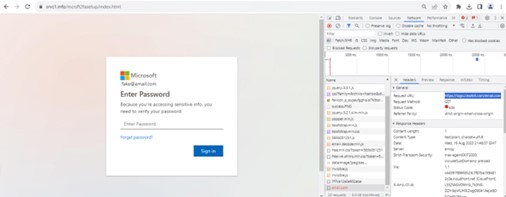
The QR codes related URL sends the person to a credential harvester masquerading as a Microsoft login web page. (See Picture 2.)
Picture 2: Credential harvester masquerading as login web page
![credential harvester looks real]()
AT&T SOC analysts analyzed the credential harvester utilizing a pretend e mail and the Google Chrome Inspector software to document any outbound connections when clicking the “Signal In” button (see Picture 2). Just one community connection was made, which resulted in a 404 HTTP response code to the exterior area “emblem.clearbit[.]com/e mail.com.” Analysis into clearbit[.]com discovered it’s related to Clearbit B2B Advertising and marketing Intelligence, which is listed as a reputable advertising software for figuring out clients and gross sales exchanges.
Analysts used open-source intelligence (OSINT) to additional analysis the preliminary related area “srvc1[.]data” however discovered no extra data because the area was just lately bought. Additional investigation revealed that the proprietor’s id was hidden, and there was no extra information accessible. The client confirmed that neither the Clearbit nor the srvc1 exterior domains have been identified or part of regular enterprise use inside their atmosphere.
Remediation
AT&T SOC analysts labored carefully with the shopper to determine which customers had acquired the e-mail and to confirm whether or not any credentials have been submitted on the login web page. Throughout this time, the analysts offered detailed directions to the shopper on how you can shut all energetic periods and instructing them to reset person credentials. Closing all energetic periods previous to any credential resets is vital for the reason that menace actor will retain entry to the person’s account till they’re utterly logged out.
The client was additionally directed to take away the phishing e mail from all person inboxes inside their atmosphere and to dam all exterior domains related to the QR code. Analysts carried out additional evaluation of the affected person accounts to substantiate that no information had been efficiently exfiltrated and that there have been no different indicators of the e-mail being circulated internally. As soon as the incident had been totally remediated, the shopper was capable of take the teachings discovered to higher inform their groups of the hazards of phishing and malicious QR codes.
Defend your self towards malicious QR codes
Phishing assaults and credential harvesters have been in use for a while. Nevertheless, as the usage of QR codes turns into extra commonplace, take care to confirm the area {that a} QR code is related to earlier than you scan it.
Moreover, keep away from scanning the QR code together with your cellular system. Sometimes, there are much less safety measures in place on a cellular system than on a network-connected company system.