Govt abstract
Within the present cyber panorama, adversaries generally make use of phishing because the main method to compromise enterprise safety. The susceptibility of human conduct makes people the weakest hyperlink within the safety chain. Consequently, there may be an pressing want for sturdy cybersecurity measures. Phishing, which capitalizes on exploiting human conduct and vulnerabilities, stays the adversary’s best choice. To counter this menace successfully, ongoing training and consciousness initiatives are important. Organizations should acknowledge and tackle the pivotal position of human vulnerability in cybersecurity.
Throughout common enterprise hours, an alarm was generated because of a buyer’s person that had interacted with a doubtlessly malicious phishing hyperlink. This prompted a radical investigation carried out by analysts that concerned leveraging a number of Open-Supply Intelligence (OSINT) instruments resembling VirusTotal and URLscan.io. Via a meticulous examination, analysts had been in a position to unveil suspicious scripts inside the phishing webpage’s Doc Object Mannequin (DOM) that pinpointed an try to exfiltrate person credentials. This detailed evaluation emphasizes the significance of proactive cybersecurity measures and showcases the effectiveness of analysts leveraging OSINT instruments together with their experience to precisely assess threats inside buyer’s environments.
Investigation
The alarm
The Managed Detection and Response (MDR) Security Operations Center (SOC) initially obtained an alarm triggered by a doubtlessly malicious URL {that a} person obtained of their inbox. Workplace 365’s menace intelligence feed flagged this URL as doubtlessly malicious. The preliminary steps in addressing this alarm contain two key actions.
First, it’s essential to find out the scope of impression on the client’s surroundings by assessing what number of different customers obtained the identical URL. Second, a radical validation course of is important to verify whether or not the URL is certainly malicious. These preliminary steps lay the muse for a complete response to safeguard the safety of the surroundings.
![Phishing alarm]()
To find out what number of customers obtained the identical URL, a complete search inside the buyer’s surroundings revealed that no different customers obtained the identical URL. Consequently, just one person is affected, suggesting that that is an remoted incident and doesn’t seem like a part of a focused assault on the client’s surroundings. With this understanding, the main target can now shift to the second step: Validating the popularity of the URL.
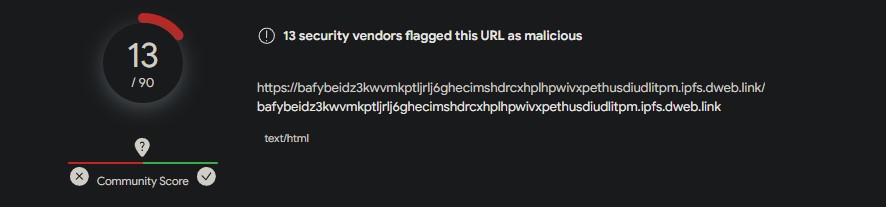
By using the OSINT instrument VirusTotal and inputting the URL obtained by the person, we intention to evaluate its potential menace stage. VirusTotal aggregates outcomes from numerous safety distributors to supply a complete evaluation. Within the present analysis, 13 out of 90 safety distributors classify this URL as malicious. It is necessary to notice that whereas the variety of distributors flagging the URL is a key issue, a conclusive dedication of malicious intent sometimes considers a consensus amongst a good portion of those distributors. A better variety of detections by various safety platforms strengthens the boldness in labeling the URL as malicious.
![VT phising - 13 vendors]()
With a doubtlessly malicious URL recognized, it’s crucial to delve deeper to establish the underlying causes for its malicious popularity. Analysts will make the most of a instrument resembling URLscan.io for this objective. URLscan.io serves as a sandbox, offering a risk-free surroundings for visiting web sites. This instrument is instrumental in conducting a radical examination to uncover the nuances contributing to the URL’s malicious classification.
After coming into our recognized malicious URL into URLscan.io, we will study the webpage meant for our buyer’s person. Upon visiting this URL, a PDF file is ready for person obtain. Nevertheless, a mere screenshot of the webpage is inadequate to supply a definitive popularity. To acquire extra perception, we should delve deeper into the webpage by analyzing its DOM.
![Webpage DOM]()
The DOM contains the important elements of a webpage, encompassing HTML, CSS, and JavaScript that outline the construction, presentation, and conduct of the web page. URLscan.io facilitates a handy examination of the DOM. In reviewing the DOM, explicit consideration is given to figuring out any malicious scripts that could be current. The main focus is usually on trying to find the HTML tags, which denote script parts inside a webpage.
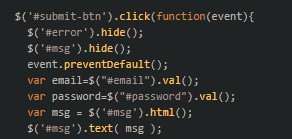
Within the analysis of the DOM related to the doubtless malicious URL, a number of tags are noticed. Inside these tags, it turns into obvious that upon the person’s interplay with the “obtain all” button, a immediate will request them to enter their e-mail and password.
![phishing script]()
That is the beginning of the script that defines the e-mail and password variables.
Persevering with by way of the script, extra regarding code emerges. Whereas the person is prompted to enter e-mail and password info, it turns into obvious that the adversary has crafted code designed to falsely declare that the entered e-mail and/or password is inaccurate, even when it isn’t. This conduct aligns with typical phishing actions, the place malicious actors try to induce customers to enter their credentials a number of instances. This tactic goals to take advantage of potential typos or errors within the entered info, guaranteeing that the adversary finally obtains the proper credentials from the sufferer.
![obtaining correct credentials script]()
After the person submits their credentials, the person’s e-mail and password are transmitted to the web site “hxxps://btmalta.cam/wefmail/e-mail (1).php” by way of an AJAX POST request. Within the context of internet improvement, an AJAX (Asynchronous JavaScript and XML) POST is a method that permits information to be despatched to a server asynchronously with out requiring a web page refresh. Sadly, malicious actors exploit this performance to surreptitiously transmit delicate person info, as noticed on this occasion.
Conducting OSINT on the aforementioned web site (“hxxps://btmalta.cam/wefmail/e-mail (1).php”) reveals a malicious popularity, notably marked by its comparatively current creation, being solely 80 days outdated from the registry date. The registration age of a site is a helpful think about assessing its credibility. On this case, the mix of a newly registered area and indications of malicious exercise raises vital considerations. It strongly means that the adversary is probably going using this area to gather the user-entered e-mail and password intentionally.
Contemplating the aforementioned particulars, it turns into extra evident that it is a credible phishing try concentrating on one in all our prospects’ customers. The tactic of information transmission, the malicious popularity of the area, and its current registration collectively underscore the severity of the scenario.
Buyer interplay
After the findings had been noticed, an investigation was created for the client to overview. If the client’s affected person entered any credential info, this implies the person account needs to be thought of compromised. Since this affected a person inside the prospects Office365 surroundings, it was advisable for the client comply with the rules set by Microsoft in an occasion of an e-mail account compromise: Responding to a compromised email account
Learn how to fight in opposition to phishing makes an attempt
Within the ongoing battle in opposition to phishing makes an attempt, implementing efficient methods is paramount to fortifying cybersecurity defenses. Listed under are a few of the many key practices and countermeasures to safeguard your group from falling sufferer to malicious phishing actions.
- Be sure that customers undergo common safety coaching to study in regards to the risks of potential phishing makes an attempt.
- Make use of processes that permit customers to report potential phishing emails that they obtain.
- Guarantee customers are correctly using Multi-Issue Authentication (MFA)
- Guarantee sturdy password insurance policies are in place to forestall any weak or insecure passwords from getting used.
- To examine to see in case your password or e-mail has ever been concerned in an information breach you need to use the free instrument https://haveibeenpwned.com/ to examine.